To Open or Not to Open an Email – Avoid Letting a Virus Into Your Office With This Phishing Email Decision Tree
by Dan Stoy, Solutions Specialist // Managed Network Services on Aug 14, 2018 3:54:02 PM
Phishing attacks are becoming increasingly targeted as cybercriminals learn to use marketing principles to personalize their emails. Unsuspecting people open these emails, click on links or open documents that seem legitimate, and open the door for a virus or ransomware to ransack the …
Hackers are Lazy – Why Are You Making Life Easy for Them?
by Dan Stoy, Solutions Specialist // Managed Network Services on Aug 1, 2018 2:36:21 PM
It's a fact that most criminals just don't want to work all that hard. Burglars would rather enter through an unlocked door or window than attempt a break in. “The overwhelming number of burglars are unskilled people who go through open or unlocked windows and doors,” says Leonard Sip …
Why Mock Phishing Might Catch You More Grief Than Good With Your Employees
by Dan Stoy, Solutions Specialist // Managed Network Services on Jul 18, 2018 3:57:09 PM
Technology has seeped into all areas of our lives — remote work environments, cell phones, appliances, doorbells, even some thermostats have wireless connectivity. This makes the sheer number of devices a single person manages on a daily basis a little overwhelming. And, with so many …
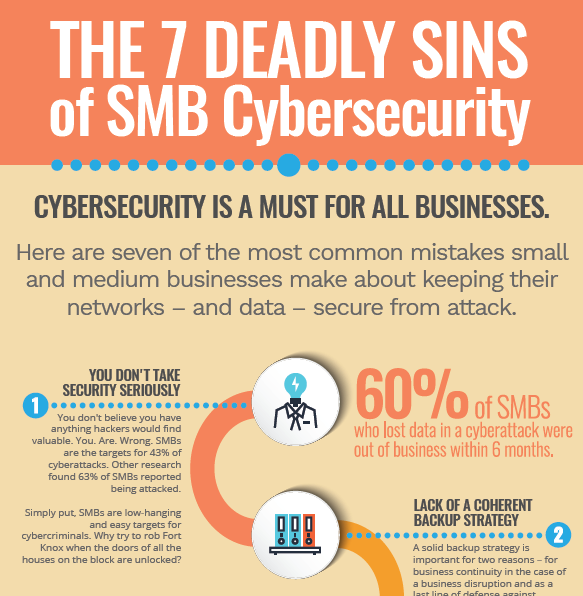
7 Deadly Sins of SMB Cybersecurity [Free Infographic]
by Dan Stoy, Solutions Specialist // Managed Network Services on Jul 11, 2018 4:31:59 PM
Information security pitfalls are everywhere. It's no fun to read blog posts all the time. So to take a break, we've put together an easy-to-read infographic to visually show you the seven most deadly sins of cybersecurity! We don't think that's hyperbole. Many small and medium busine …
I Have an IT Staff – I Don't Need a Managed IT Partner to Help Secure and Manage My Network
by Dan Stoy, Solutions Specialist // Managed Network Services on Jul 6, 2018 12:47:29 PM
Your business, our business, your competition's business, everyone's business today relies on a secure, scalable IT network and an IT infrastructure that supports business goals and allows a company to thrive. Offices that don't secure their networks and business information are putti …
How Much Will a Data Breach Cost You? It Depends
by Dan Stoy, Solutions Specialist // Managed Network Services on Jun 22, 2018 1:46:42 PM
We've written about security quite a bit – and our open house last month was focused on security topics. As we bring more managed network services to you, we'll continue to focus on security issues – risk, cost, tips, etc. Most business leaders we talk to understand, at least generall …
Some Day Your Nigerian Prince Will Come – 9 Simple Tips to Dodge Phishing Emails
by Dan Stoy, Solutions Specialist // Managed Network Services on Jun 20, 2018 8:10:00 AM
Even companies that do everything right when they built their security infrastructure can still be hacked. The sad fact is, the weak point in every cybersecurity system is you and the people you work with. Hacks and data breaches do occur because of disgruntled employees. The majority …
Do You Have the Time and Expertise to Manage Network Security Yourself?
by Dan Stoy, Solutions Specialist // Managed Network Services on Jun 15, 2018 2:25:23 PM
What's the best use of your IT staff's time? Companies increasingly have the option to hire IT expertise to handle their IT infrastructure – from your website to your hardware to your servers to your network security, there is an service provider that can do it for you. Why would you …
Fear, Information Security, and Chicken Little
by Dan Stoy, Solutions Specialist // Managed Network Services on Jun 12, 2018 8:05:00 AM
When we started to include managed networks into our services for clients, we immediately realized how serious an issue cybersecurity is. The amount of malware in the world and the tenacity of cybercriminals is stunning. A research report written by CSIS and sponsored by McAfee puts t …