Share this
Some Day Your Nigerian Prince Will Come – 9 Simple Tips to Dodge Phishing Emails
by Dan Stoy, Solutions Specialist // Managed Network Services on Jun 20, 2018 8:10:00 AM
Even companies that do everything right when they built their security infrastructure can still be hacked.
The sad fact is, the weak point in every cybersecurity system is you and the people you work with.
Hacks and data breaches do occur because of disgruntled employees. The majority of employee-caused data breaches result from negligence or ignorance. Even if the following data breach is unintentional, the potential costs are real.
How can you further protect your office?
Training.
Organizations are beginning to invest in training their users in security best practices. Recent research from Aberdeen Group shows that 91% of companies performing security awareness and training were trying to reduce cybersecurity-related risk from user behaviors.
Phishing on the Rise

Wombat Security has an annual “State of the Phish Report.” The 2018 edition shows a continued climb in attacks (similar reports from others reveal the same overall trend). From the report:
- 76% of organizations said they experienced phishing attacks in 2017
- Nearly half of information security professionals said the rate of attacks increased from 2016 to 2017
- In 2017, there was an 80% increase in reports of malware infections, account compromise, and data loss related to phishing attacks
The research also reveals that regular, interactive training (monthly or quarterly) is twice as effective at achieving quantifiable benefits than yearly or passive training tools (email alerts, company newsletters, or videos).
What's Phishing Again?
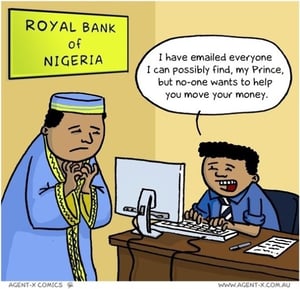 Those of you reading this who began using email in the early 1990s remember the Nigerian prince. All he needed was you to open a bank account (with at least $10,000 in it) and you would then receive a percentage of the windfall from the Nigerian prince's new oil money! Or you need to some some personal information and documents to get your lottery winnings (from a foreign country and a lottery you had never entered). The scam varies slightly.
Those of you reading this who began using email in the early 1990s remember the Nigerian prince. All he needed was you to open a bank account (with at least $10,000 in it) and you would then receive a percentage of the windfall from the Nigerian prince's new oil money! Or you need to some some personal information and documents to get your lottery winnings (from a foreign country and a lottery you had never entered). The scam varies slightly.
The most disturbing part of that phishing attack is that it must work because it's still going on!
Here's the Wikipedia definition:
Phishing is the attempt to obtain sensitive information such as usernames, passwords, and credit card details (and money), often for malicious reasons, by disguising as a trustworthy entity in an electronic communication. The word is a neologism created as a homophone of fishing due to the similarity of using a bait in an attempt to catch a victim. According to the 2013 Microsoft Computing Safety Index, released in February 2014, the annual worldwide impact of phishing could be as high as US$5 billion.
Phishing is typically carried out by email spoofing or instant messaging, and it often directs users to enter personal information at a fake website, the look and feel of which are identical to the legitimate one and the only difference is the URL of the website in concern. Communications purporting to be from social web sites, auction sites, banks, online payment processors or IT administrators are often used to lure victims. Phishing emails may contain links to websites that distribute malware.
Protect Yourself and Your Office
Creating an ongoing training plan will continually reinforce the importance of security, but what can you do today?
The best tip is an obvious one – if an email/offer in an email sounds too good to be true it almost certainly is! Never share personal details based on an email received out of the blue.
Here are 9 basic tips to get you started:
- We are all overloaded with emails today. Be skeptical about out-of-the-blue offers. As we all share more information on social channels, cybercriminals use that information to craft more sophisticated phishing messages. The first line of defense is to not be gullible.
- When you receive a request to transfer funds, open an attachment (especially from an unexpected email address), or provide sensitive information; don't do it immediately. When providing sensitive information, it's best to go directly to the site yourself rather than click on a link. Many links will look nearly identical to a legitimate URL – nextflix.com for example, being off by one or two letters. If unsure, hover over the URL with your mouse and check it out before clicking. Pay attention to sites as you're browsing as well. If there's anything before the common endings – .com, .edu, .net, etc. – you're cache may be compromised. If you see anything like www.netflix.ad.com, contact your IT staff ASAP.
- Backup your data. As I've written before, ransomware is often delivered through a phishing email. Data backup provides a last line of defense.
- It's not just email. Beware of social media and Web browser links too.
- Use anti-phishing and anti-ransomware solutions as part of your security infrastructure.
- Control the use of personal devices that access corporate systems. If you allow BYOD, ensure that those devices are included in your security infrastructure.
- Ensure that all employee software and operating systems are kept updated. Malware often exploits known security holes that have already been patched – be sure to apply patches and updates regularly!
- Look for grammar mistakes. While everyone has a typo now and then, many phishing emails will have multiple basic spelling and grammatical errors.
- Have regular staff security training and make security a priority in your office from the top down.
While your people are your last line of defense against phishing, you need a solid security infrastructure in place as a first line to defend against malware and prevent data breaches.
Managed network services is a possible solution for many businesses. Part of Coordinated's services include a network assessment to determine how secure your office really is. Contact us for a free consultation and assessment.
Share this
- February 2026 (1)
- January 2026 (1)
- December 2025 (1)
- June 2025 (1)
- March 2025 (1)
- February 2025 (1)
- January 2025 (4)
- October 2024 (1)
- July 2024 (1)
- June 2024 (4)
- May 2024 (4)
- April 2024 (4)
- March 2024 (5)
- February 2024 (4)
- January 2024 (4)
- December 2023 (1)
- November 2023 (4)
- October 2023 (4)
- September 2023 (4)
- August 2023 (4)
- July 2023 (4)
- June 2023 (5)
- April 2023 (2)
- March 2023 (1)
- February 2023 (2)
- January 2023 (2)
- May 2022 (1)
- April 2022 (3)
- March 2022 (1)
- February 2022 (1)
- December 2021 (2)
- October 2021 (2)
- July 2021 (1)
- June 2021 (1)
- April 2021 (2)
- March 2021 (2)
- February 2021 (1)
- January 2021 (2)
- December 2020 (1)
- November 2020 (1)
- October 2020 (2)
- August 2020 (2)
- July 2020 (2)
- June 2020 (2)
- May 2020 (1)
- April 2020 (2)
- March 2020 (4)
- February 2020 (4)
- January 2020 (4)
- December 2019 (3)
- November 2019 (5)
- October 2019 (3)
- September 2019 (4)
- August 2019 (3)
- April 2019 (4)
- March 2019 (2)
- February 2019 (3)
- January 2019 (4)
- December 2018 (4)
- November 2018 (6)
- October 2018 (5)
- September 2018 (10)
- August 2018 (7)
- July 2018 (5)
- June 2018 (8)
- May 2018 (10)
- April 2018 (10)
- March 2018 (7)
- February 2018 (6)
- January 2018 (8)
- December 2017 (7)
- November 2017 (8)
- October 2017 (7)
- September 2017 (7)
- August 2017 (7)
- July 2017 (3)
- June 2017 (5)
- September 2015 (1)
- June 2014 (1)


Comments (2)